The report, titled Microsoft Digital Defense Report 2023 says:
"Russia-affiliated threat groups engaging in influence campaigns continue to try to sow distrust between Ukrainian populations and European partners who support Kyiv — both governmental and civilian. One of the more prominent cyber-enabled influence campaigns targeting populations outside of Ukraine involved a series of operations showing similar TTPs [tactics, techniques and procedures] as those used by Storm-0257 (a threat group Microsoft assesses as most similar to Ghostwriter and UNC1151).
"The campaign appeared aimed at diminishing trust between the Ukrainian diaspora and refugees, Polish, Lithuanian, and Latvian populations, and their governments.
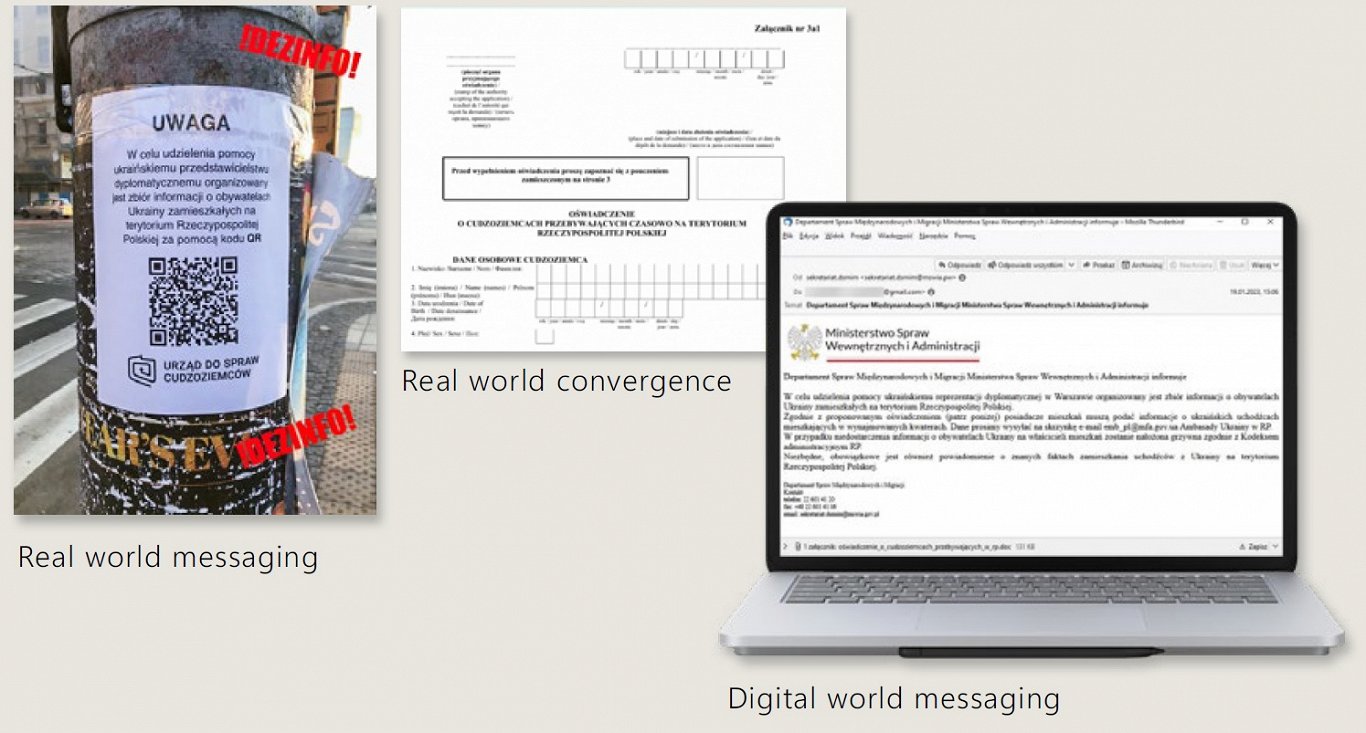
"The campaign, which was first observed around mid-January 2023, leveraged email dissemination and inauthentic documents to spread a narrative that government officials may seek forced repatriation of Ukrainians or conscript European citizens for the war in Ukraine. Populations in NATO member states Poland, Latvia, and Lithuania were the primary targets.
Microsoft’s investigation uncovered that one of the documents distributed via email was also tied to a physical flyer posted in Poland, demonstrating that the campaign bridged the digital and physical worlds. The Polish-language, pro-Russia website Dziennik Polityczny, Belarusian state television, and a network of sockpuppet accounts posing as Lithuanian citizens on social media served to further amplify the messages, the report said.
In addition, Microsoft said it has observed instances of convergence between Russia-affiliated cyber operations and pro-Russian “hacktivist” attacks in Ukraine that probably serve to obscure Russian state involvement.
"Seashell Blizzard, Cadet Blizzard, and other suspected Russian actors all conducted operations that at times shared victimology and close temporal proximity with hacktivist groups that leaked sensitive stolen data or claimed to have conducted cyberattacks against named organizations.10 Cyberenabled influence campaigns involving purported hacktivist groups Cyber Army of Russia, Free Civilian, and others almost certainly served to discredit the victim organizations, while the public claims of responsibility likely aimed to amplify the effects of cyberattacks on victims’ networks," Microsoft said.
The computing giant also agreed with many western politicians' suspicions that Russia is trying to "turn support for Ukraine into a point of conflict between Western populations and their governments".
"Russian state-sponsored influence actors, organizations, and outlets have helped amplify, support, and even organize pro-Russian, antiwar protests across Europe. For example, Russia’s ruling party, United Russia, has nurtured ties with figures and groups within Italy’s pro-Russia, anti-Ukraine war movement, while the Kremlin has tried to influence and steer protests in Germany and forge an antiwar political coalition.
"Pro-Russian influence operators have specifically aimed to disrupt Western military support to Ukraine by encouraging European citizens to demonstrate against military assistance," says the report.
"We assess with moderate confidence that a protest initiative out of Western Europe called “Stop Killing Donbass” is a continuation of an earlier protest initiative known as the “Map of Truth.” Both initiatives tried to convince Europeans that Western military aid to Ukraine helps Kyiv kill innocent noncombatants, particularly children, and the two share striking similarities in TTPs, intended audience, involved individuals, and connections to a cluster of obscure websites," it asserted.
The full report is available at: https://www.microsoft.com/en-us/security/security-insider/microsoft digital-defense-report-2023. In addition, Microsoft has this handy guide to current Russian cyber threat trends: https://www.microsoft.com/en-us/security/business/security-insider/threat-briefs/7-emerging-hybrid-warfare-trends-from-russias-cyber-war/